How it Works
A secure, cloud-centric privilege access management platform provisioning access to users through a self service portal.
Simplify Cloud IAM Complexity
Learn more about how Procyon solves Multi-Cloud Privilege Access Management (PAM).
Nothing to Remember, Nothing to Steal
Procyon eliminates credential sprawl with a next-generation, passwordless approach that secures your critical infrastructure without slowing down developers.
Trusted Platform Module offers a strong security property – the private key stored in the chip can’t be read.
The Procyon controller and authenticator app work together to provide Just-In-Time access to cloud resources.
Procyon Self Service Portal available on:
MacOS
Windows
iOS
Android
How vulnerable is your organization to credential sprawl?
Discover potential vulnerabilities now with our Assessment tool and understand how Procyon can help you solve the problem in a matter of hours.
Recent Resources
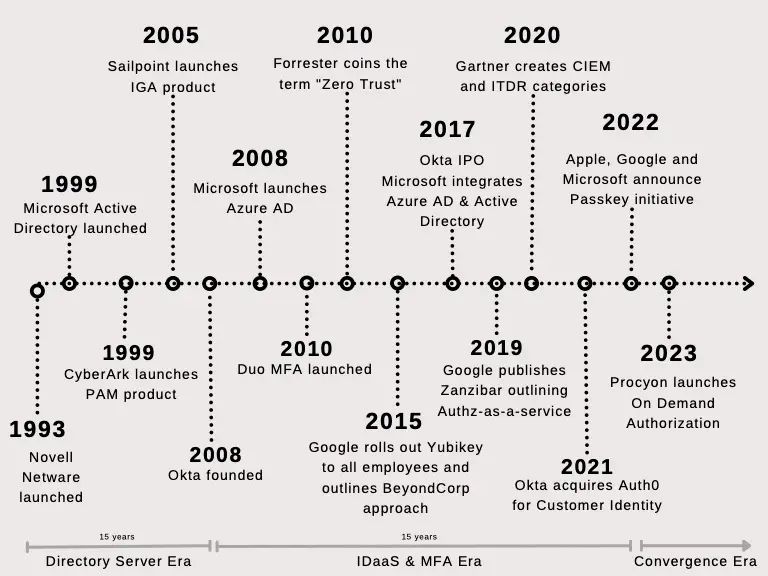
Identity and access management traces its roots back to the mainframe era. DoD first employed logical...
Image credit: Unsplash Passkeys are emerging as a popular passwordless phishing resistant authentication technology....
Image credit: Unsplash Ken Thompson the creator of Unix operating system and C programming language gave his now...
Get in touch
Want to know more about our product? Please fill out the form and share your message with us.
- Request a demo
- Business tiers and pricing
- General questions