Go Passwordless with Procyon Privilege Access Management (PAM)
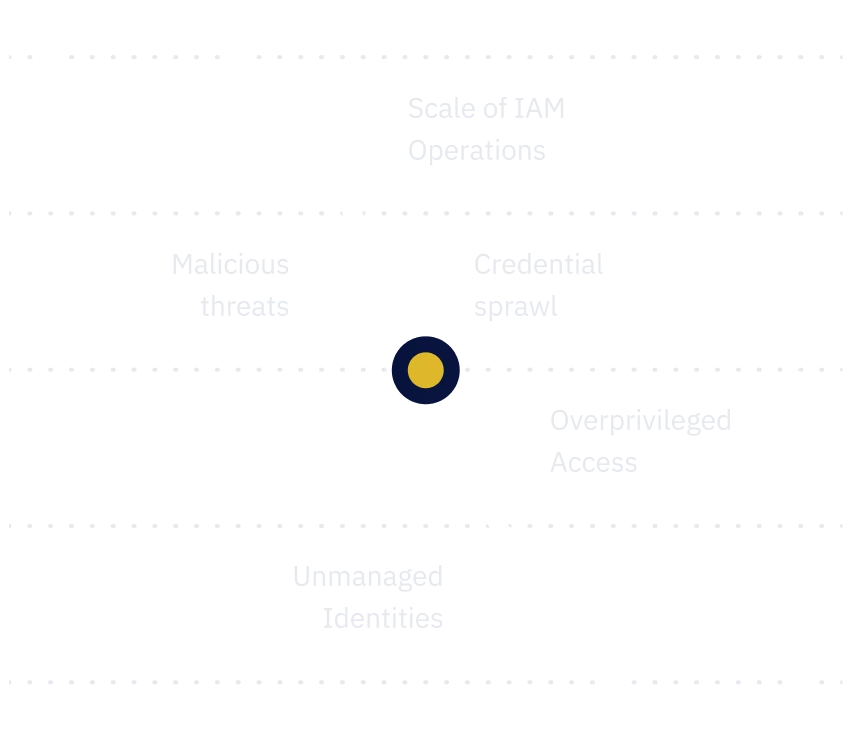
Scale faster and stop credential sprawl by eliminating shared accounts and static credentials that are challenging to track.

TPM Security
Procyon leverages a TPM (Trusted Platform Module) chip on modern laptops. The Procyon solution strongly identifies the user and device using the TPM chip, ensuring every transaction is authenticated and authorized continuously.
Stop Data Breaches
Bad actors on the internet don’t break in, they just sign into your accounts. With Procyon, developers and security teams don’t have to worry about credential theft as there are no real credentials stored. AWS, GCP, Azure, and other cloud native tools work seamlessly.
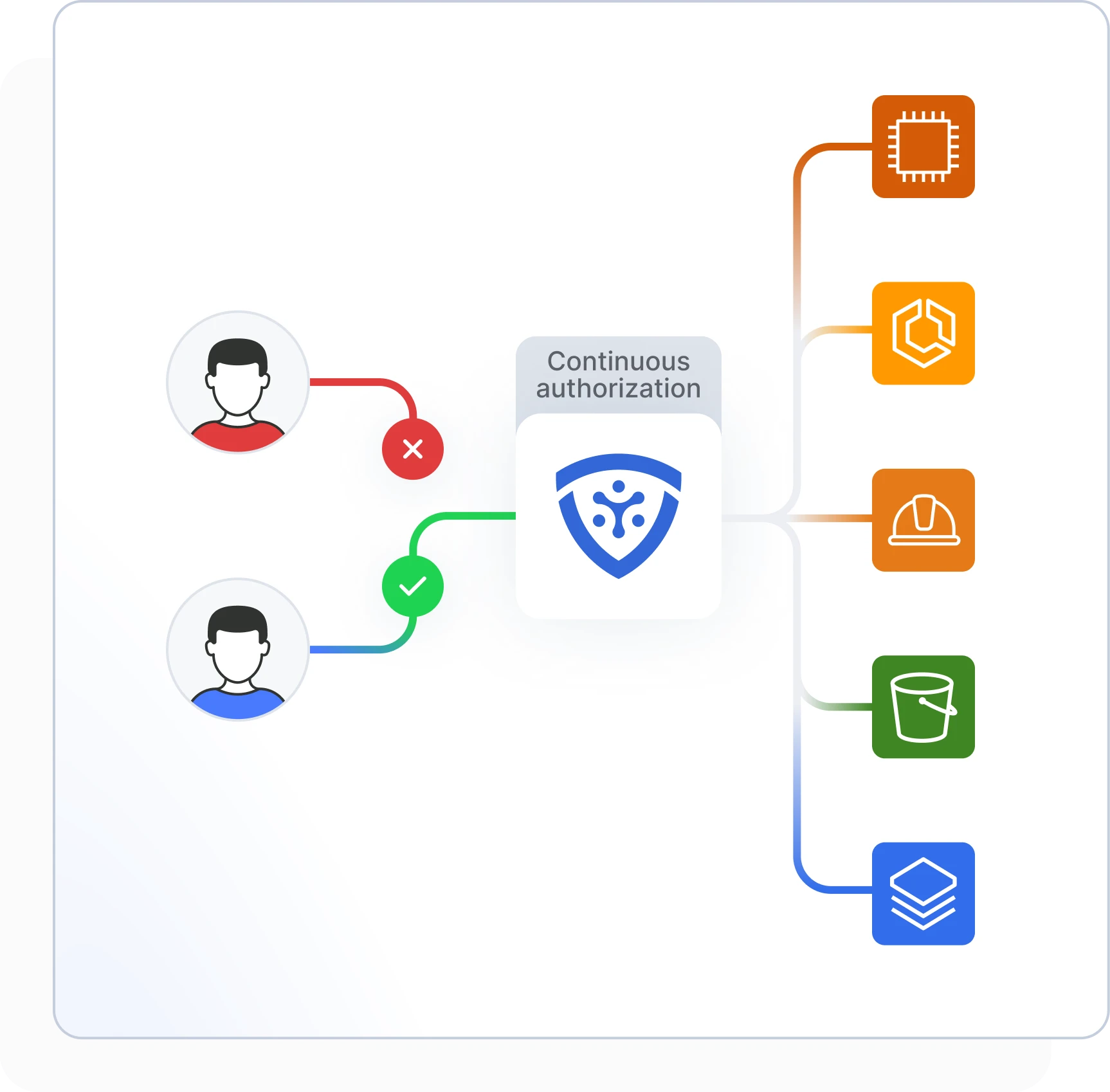
Passwordless Access for Developers
Passwordless authentication offers users a way to verify themselves without having to remember or manually type passwords. This provides stronger security and fewer breaches. Users can conveniently and securely access applications and services using biometric solutions.
How vulnerable is your organization to credential sprawl?
Discover potential vulnerabilities now with our Assessment tool and understand how Procyon can help you solve the problem in a matter of hours.
Recent Resources
Get in touch
Want to know more about our product? Please fill out the form and share your message with us.
- Request a demo
- Business tiers and pricing
- General questions