Meet Compliance Requirements for Your Cloud Infrastructure

Maintain Continuous Compliance
Comprehensive Protection Through Least Privileged Access

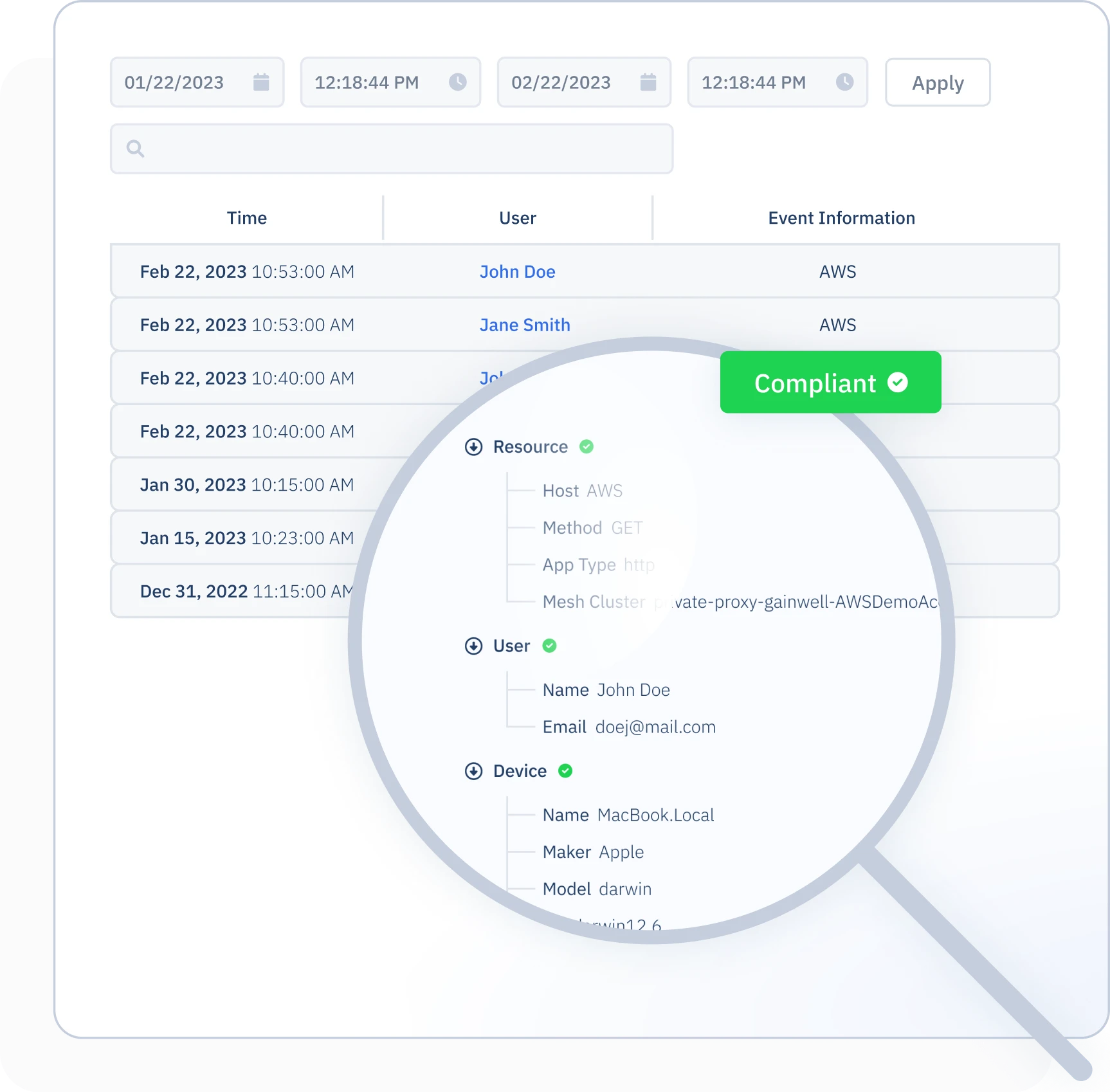
Digging Deeper Into Your Audit Logs
How vulnerable is your organization to credential sprawl?
Discover potential vulnerabilities now with our Assessment tool and understand how Procyon can help you solve the problem in a matter of hours.
Recent Resources
The Sisense Breach: Why Strengthening Credential Security is Priority In today's interconnected digital landscape,...
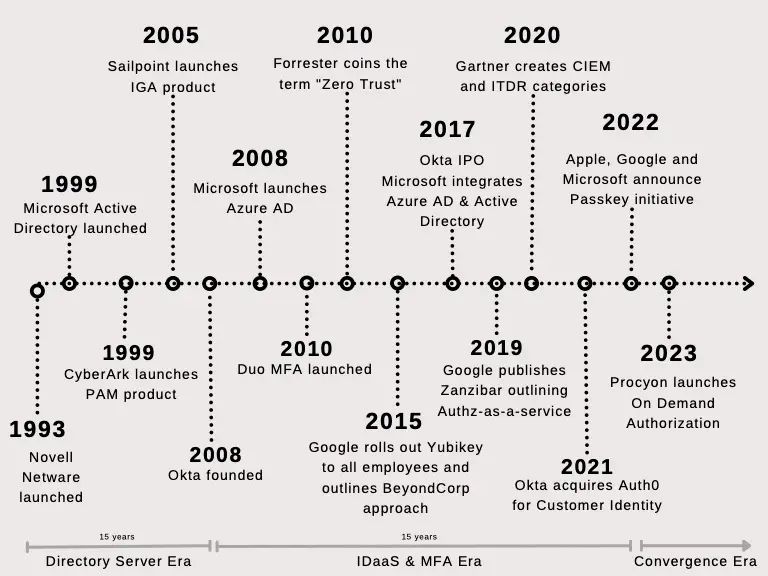
Identity and access management traces its roots back to the mainframe era. DoD first employed logical...
Image credit: Unsplash Passkeys are emerging as a popular passwordless phishing resistant authentication technology....
Get in touch
Want to know more about our product? Please fill out the form and share your message with us.
- Request a demo
- Business tiers and pricing
- General questions